Penetration Testing (PT)
Simulate Real-World Attacks to Validate Your Defenses

What is Penetration Testing?
Penetration Testing (or "Pen Testing") is an authorized, simulated cyberattack on your computer system, performed to evaluate its security. Unlike vulnerability assessments which simply list potential issues, our certified ethical hackers actively attempt to exploit these weaknesses just like a real attacker would, to demonstrate the true impact of a breach.
This hands-on approach validates whether your existing defenses can withstand a sophisticated, targeted assault and helps you fix critical flaws before they are weaponized.
Ethical Hacking
Our experts use the same tools and techniques as malicious hackers, but in a safe, controlled environment.
Targeted Exploitation
We go beyond scanning to actively exploit vulnerabilities, proving exactly how deep an attacker could get.
Defense Validation
Test the effectiveness of your firewalls, intrusion detection systems, and security policies against real threats.
Compliance Proof
Meet strict regulatory requirements (PCI-DSS, HIPAA, ISO 27001) that mandate regular manual penetration tests.
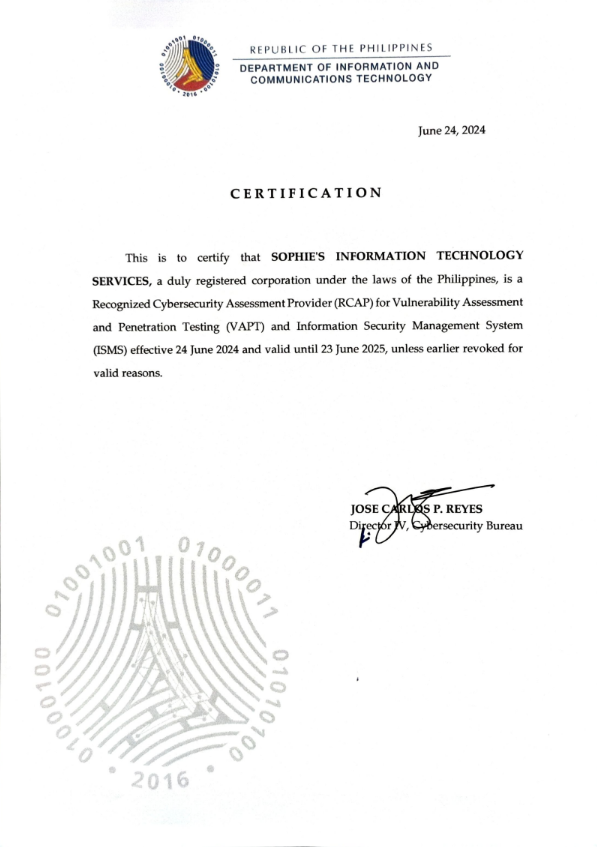
Our Accreditations